With the number of types of smart devices from rfid chips to thermostats and even kitchen appliances growing so quickly they can t always be monitored.
Mobile device security threats and controls.
But the truth is there are different types of mobile security threats to be aware of.
The internet of things iot.
Worms and spyware unauthorized access phishing and theft.
People tend to look at mobile security threats as an all encompassing threat.
They include application based web based network based and physical threats.
Mobile security threats explained.
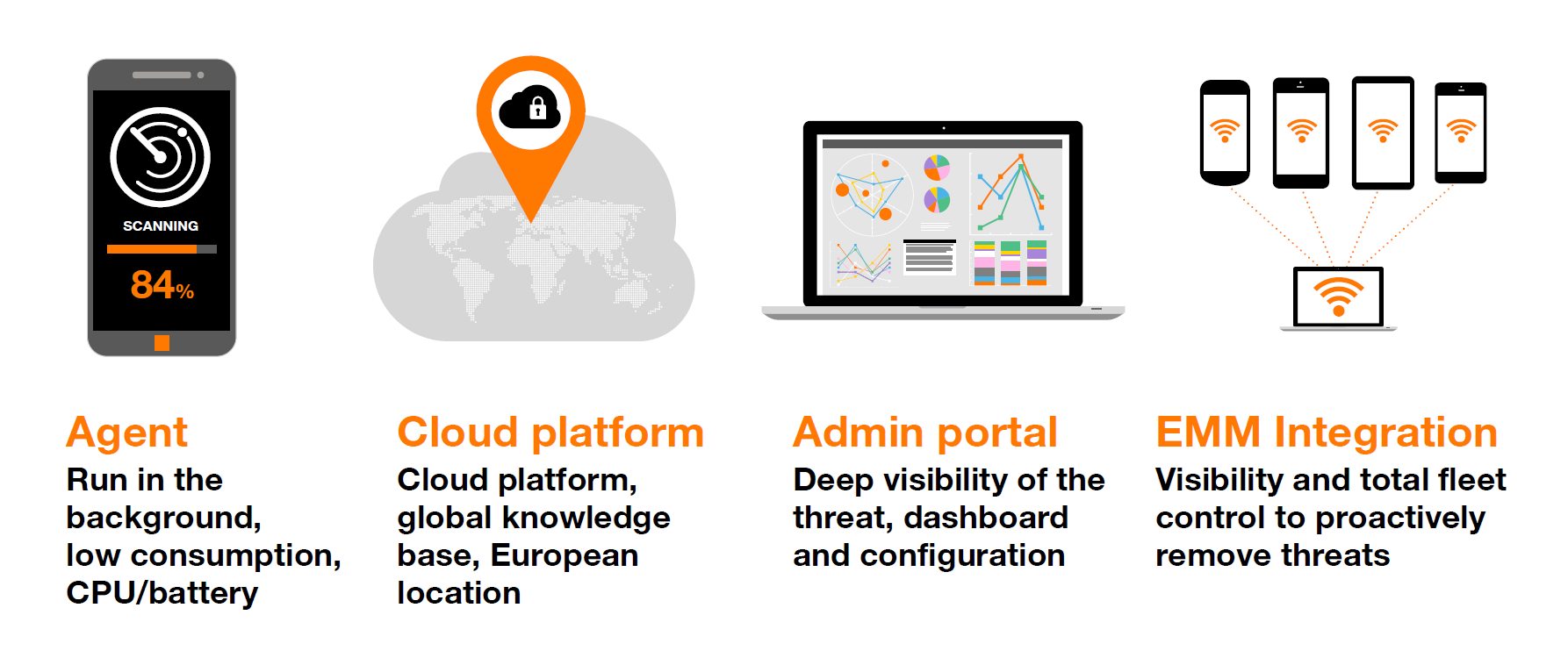
Learn about the enterprise mobile device security controls including malware defense threat detection and centralized management that you should consider when formulating an enterprise.
Here s how they work.
Application based threats web based threats network based threats and physical threats.
We divide these mobile threats into several categories.
Here are some practical steps that will help you minimize the exposure of your mobile device to digital threats.
However personal mobile devices don t offer the same level of built in security or control as the organization owned desktop computers they are replacing.
Some of the security threats include malware specifically designed for mobile devices i e.
This is exactly where google and apple lack control he adds.